This post, intended for this site, originally appeared in my blog due to crippling DDoS attack. Do read updates about Rosneft at end of post. It was busy last week. As I was chatting to a source in Caracas last Monday, I noticed that this site was down. Asked my web host (shout out to the excellent folks at LeaseWeb), and was informed that -yet another- DDoS attack had been launched against us. This is the third time a DDoS attack has been directed to my websites: once at vcrisis.com and twice at infodio.com.
I must wonder, of course, at the reasons. Why would anyone seek to prevent the general public from learning about the stuff I publish here? Is it because we expose Venezuela's rampant corruption? For those who are yet to get acquainted with the situation, Venezuela is a Spanish speaking country, of some 30 million. It is, after 17 years of chavista rule, a failed nation in the fullest sense of the term. But this site does not cater for a Venezuelan readership. It seeks to inform the wider world about who's who in the Boliburgeoisie, a new extremely wealthy and, equally, extremely inept class of 'businessmen' that could only become minted under the shadow of Hugo Chavez's so called socialist revolution. We talk about the Alejandro Betancourts of this world, the Juan Carlos Escotets, the Victor Vargas, the Danilo Diazgranados, the Francisco D'Agostinos and Luis Obertos... we investigate the origin of their newly found riches, we track their operations across many different jurisdictions, we expose those who enable, aid and abet them, like Adam Kaufmann and Glenn Simpson, the Al Cardenas, or even Baltazar Garzon, we uncover their deals, in Africa, Europe, Russia, Asia, in sum, we shed a glimmer of sunlight on their otherwise opaque underworld.
It is, therefore, to be expected that such work would attract the ire of nasty, criminal, yet extremely resourceful thugs (dirty money is welcomed by everyone everywhere nowadays). Dealing with this lot exposes us to very dangerous vendettas. They operate in a world without border / immigration barriers. They criss-cross the globe in their own private jets: one day they're having Heston Blumenthal cooking for them, the next they're in St. Barths hanging with Roman Abramovich, and the third meeting with ex-WSJ hacks, former Manhattan prosecutors and leaders from America's GOP, when not cavorting with the very best of Sloanes in London. Their reach knows no constraints either. A London raid can be easily organized from Caracas, without as much as a worry of ever getting caught. That's the kind this site deals with.
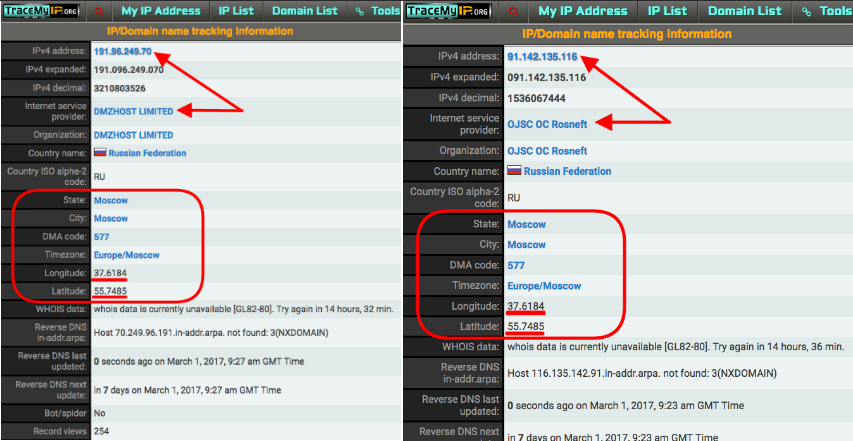
The latest comes from Russia, or more specifically, an IP address controlled from Russia (191.96.249.70). A vulnerability in the Wordpress blogging platform allows the pingback method to be used to launch DDoS attacks (explanation here). Basically, someone makes use of that vulnerability to ping a target website. Checking my server logs, I noticed the following pattern:
- "GET / HTTP/1.1" 200 32295 "http://infodio.com/" "WordPress/4.7.2; https://www.customescaperoom.com; verifying pingback from 191.96.249.70"
- "GET / HTTP/1.1" 200 32293 "http://infodio.com/" "WordPress/4.6.3; http://www.toptasting.com; verifying pingback from 191.96.249.70"
- "GET / HTTP/1.0" 200 145833 "-" "WordPress/4.0.15; http://wisecleaner.online; verifying pingback from 191.96.249.70"
When that request is repeated many thousands of times per second servers tend to collapse due to increased traffic, as was the case with mine. Thousands of such requests, as well as POST and HEAD requests, were launched from servers around the world.
However, IP 191.96.249.70, as all others, is associated to a host provider, in this case DMZHOST.CO. Said domain, as all others, is in turn registered by a person, somewhere, in this case a Christian P, with an address in the Seychelles very similar to that of Mossack Fonseca (Oliaji Trade Centre, Francis Rachel Street, Victoria Mahe, Seychelles).
Every domain has to have a person or organization responsible. In the case of DMZHOST.CO it initially had Dmzhost Limited as responsible party, but seems to have passed control to JUPITER 25 LIMITED. A search for Jupiter brings us closer to home, to 35 Firs Avenue, N11 3NE, London, United Kingdom. Please do note, in the last link, that there's a chris@dmzhost.co as contact for Jupiter. Could this be the same person as Christian P in the Seychelles?
There are hundreds of companies registered in 35 Firs Avenue. According to Companies House data, Darren Symes is Jupiter's director, Symes is associated with over 200 companies. Others folks investigating similar attacks have had this to say about DMZHOST in the recent past:
“Bulletproof hosting” providers like DMZHOST provide VPSs that advertise themselves as outside of the reach of Western law enforcement. DMZHOST offers its clients “offshore” VPSs in a “Secured Netherland datacenter privacy bunker” and “does not store any information / Log about user activity.” At the same time, DMZHOST’s terms of service are just as concise. “DMZHOST does not allow anything (related) to the following content: – DDos – Childporn – Bank Exploit – Terrorism – NO NTP – NO Email SPAM”.
Further investigation of IP 191.96.249.70 and Jupiter 25 Limited indicate that its DNS servers are controlled by yet another London-based company: Host1Plus. This one in turn seems to be a trading name of Digital Energy Technologies Ltd.
Bitcoin payments, obscuring identity of ultimate culprits, are readily accepted by both DMZHOST and Host1Plus. I sent a tweet to Host1Plus' Vincentas Grinius, that was replied in the most ridiculous fashion to avoid dealing with the actual DDoS question.
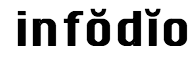
I also sent an email request to chris@dmzhost.co, and got an almost immediate reply,* asking for logs. Chris sends emails from somewhere around Pavia in Italy (93-36-187-144.ip61.fastwebnet.it). He claims the server used for DDoS attack "has been shutdown", but refuses to say who used the server, who contracted server services with his company, how did he get paid, and refuses to provide his full identity or that of his client/s. If he ever identifies himself fully, and provides proper explanations as to use of his platform to DDoS this site*, I shall add his comments here, alas I have no hope: while asking him to reconsider, my inbox has been rendered almost dysfunctional in a matter of minutes by an avalanche of spam (see below), which started after my third email to Chris. So the server "has been shutdown" alright, but the attack has morphed...
|
Despite denials, queries per second peaked minutes after |
Not all has been bad though. Right after Brian Krebs suffered the largest ever DDoS attack I remember having read about how Google had come to the rescue. Through Twitter I got in touch with Nicholas Platt, Digital Media Producer of Jigsaw, a technology incubator of Alphabet (Google's parent co). When the DDoS attack started I managed to get an invite to join Project Shield, which is the Google platform that defeated Krebs attackers. I will be forever grateful for this act of kindness, and to Ashish at Project Shield for walking me through correct set up. The folks from LeaseWeb, my web hosting provider, must also receive my public gratitude: rather than kicking me out -after all the attack caused a lot of disruption and man hours to solve, Tom, Reece and Bagata kept their Dutch cool and were tremendously helpful.
Virtual crooks are getting more brazen by the day, though I seriously doubt they will ever reach Google's levels of computing power. The silver lining is that due to the latest DDoS attack, no amount of stolen Venezuelan money will ever be able to knock this site offline again. It is yet to be determined which of the thugs normally exposed here is behind the latest attack, though we will carry on investigating, exposing, and shedding light upon corruption and the Boliburgeoisie. The latest findings put to rest the no-bid contracts given to Derwick, Diazgranados intentions to buy a sizeable portion of Compagnie Bancaire Helvetique, Charles Henry de Beaumont's dirty dealings with Oberto and other thugs in the Caribbean, the direct links between corrupt chavistas and their preferred contractors, etc.
* Right after confronting chris@dmzhost.co this afternoon, DDoS attack against infodio.com was relaunched, with the added bonus of a huge spam avalanche in my inbox. Chris claims that neither him nor his company were behind DDoS attack, and added that he "could help you on mitigating ALL attacks. We are experienced on mitigating attack since also us receice many attacks"... (sic)
Further investigations indicate that Chris' UK proxy, Darren Symes, has had a colourful past fronting for other scam artists grouped under Claremont Partnerships and Noble Rock Partners.
UPDATED 25.02.2017 13:38GMT: My server logs are providing more clues as per nature of attack. Project Shield's visits started yesterday morning:
- 104.196.28.249 - - [24/Feb/2017:10:26:29 +0100] "GET / HTTP/1.1" 200 146265 "-" "Mozilla/5.0 (compatible; ProjectShield-UrlCheck; +http://g.co/projectshield)"
This continued, more or less uninterruptedly, until early afternoon and was coupled with spidering by Google bots, etc.:
- 35.184.90.184 - - [24/Feb/2017:14:24:36 +0100] "GET / HTTP/1.1" 200 146265 "-" "Mozilla/5.0 (compatible; ProjectShield-UrlCheck; +http://g.co/projectshield)"
Then this happened:
- 104.155.70.96 - - [24/Feb/2017:14:26:09 +0100] "GET / HTTP/1.1" 200 145833 "-" "WordPress/4.4.2; http://jazzjackrabbit.org; verifying pingback from 191.96.249.54"
- 104.199.6.69 - - [24/Feb/2017:14:26:09 +0100] "GET / HTTP/1.1" 200 32299 "http://infodio.com/" "WordPress/4.7.2; https://www.virtualsunburn.com; verifying pingback from 191.96.249.54"
- 104.199.61.249 - - [24/Feb/2017:14:26:09 +0100] "GET / HTTP/1.1" 200 32299 "http://infodio.com/" "WordPress/4.6; http://pironsecurity.com; verifying pingback from 191.96.249.54"
At 14:24, chris@dmzhost.co sent an email saying:
"Do not threat since for be clear we are not who launch you the attack. And we have take immediate action suspending the server so lawfully speaking we are total ok." (sic)
About two minutes passed between his "lawfully speaking we are total ok" and the restart of DDoS and further spam avalanche. However the IP had been changed, from previous 191.96.249.70 to 191.96.249.54, both controlled by his DMZHOST company.
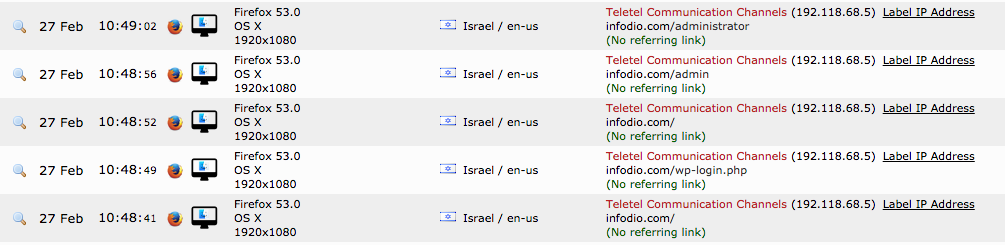
Email headers suggests that his email server (mail.ru) is located in a GMT +0300 time zone (Russia) and then routes it through Italy's Fastweb. His browser appears to be configured in Italian and he visited some of my sites from a Fastweb server at around same time:
I've sent an email to abuse@corp.mail.ru, however I have little expectation of ever getting a straightforward and appropriate reply. Added: Eventually I got reply from mail.ru, saying chris@dmzhost.co is not a registered user, despite email header evidence to the contrary.
The spamming of my inbox continues in earnest: chris@dmzhost.co did not reply my last email, I guess he did not appreciate my confronting him and details in this post. Added: two replies eventually made it to my inbox over the weekend, one from usual @dmzhost.co address and another one from dmzhosts@protonmail.com. I contacted abuse at protonmail, to try to corroborate IP location from where inbox is being accessed, but haven't received any replies. Finally revealing involvement, Chris wrote:
IF YOU ARE RECEIVING THIS MAIL ITS BECAUSE WE CANNOT REACH YOU FROM OUR MAIN MAIL. Please provide another mail which is not being spammed.. or skype account
DDoS Attacks directed to the site were still crippling functionality and access, with five outages in the last seven days. Efforts to hack into the site continue...
Google's Project Shield (protecting my site) is also protecting this guy who's exposing the plunderers of Venezuela https://t.co/GndJyeqSFT
— briankrebs (@briankrebs) February 28, 2017
UPDATE 01.03.2017 07:46GMT: Looking at the latitude and longitude details of attacking IPs 191.96.249.70 and 191.96.249.54 in Google Maps, I noticed Rosneft HQ location. Further research reveals that Rosneft.ru has exactly the same latitude and longitude details that IPs from where DDoS attack against my site were launched. Considering chavismo's relations with Russian 'state' companies, isn't that just an extraordinary coincidence?